
Learn more about SPF
I have SPF, do I need DMARC to protect my domain? What does DMARC do that SPF does not?
What SPF does
- SPF authorizes the sending IPv4/IPv6 addresses.
- SPF protects the header of the email that is not visible to the end-user (known as
Return-Path,MAIL FROM, "Envelope From", or Bounce address). If this header is missing, the SPF check will be done on theEHLO/HELOaddress.
What SPF does not
- SPF does not require any alignment between the
Fromdomain and the above-mentionedReturn-Pathaddress that it checks, meaning the two don't have to match from an SPF perspective. - SPF does not provide any reporting functionality, meaning the receiver of the email won't send back any reports to the sender, containing results of the email authentication.
- SPF does not survive auto-forwarding and indirect mail-flows.
These shortcomings prompted the introduction of DMARC to explicitly tell receivers what to do and provide authentication reports. These reports enabled the sender to take the necessary actions to fix legitimate mail flows.
DMARC makes use of SPF as one of its foundations but also adds additional features as it:
- Focuses on the
Fromheader which is visible to the end user ("Header From"). - Requires that the domain used by SPF aligns (either an exact match or subdomain) with the domain found in the visible
Fromaddress of the email. - Ignores the nuances of soft fail and hard fail in your SPF configuration i.e.
~alland-allare treated equivalently as an SPF fail. - Provides the reporting functionality to send email authentication results back to the owner of the
Fromso they can find out if their domain is being misused. It also helps with troubleshooting your deliverability as the reporting will aid in discovering any misconfiguration with your legitimate email senders. - Provides a policy that tells the receivers what to do with an email that fails email authentication. This policy is enforced by the receivers. There is no enforcement when SPF is used without DMARC.
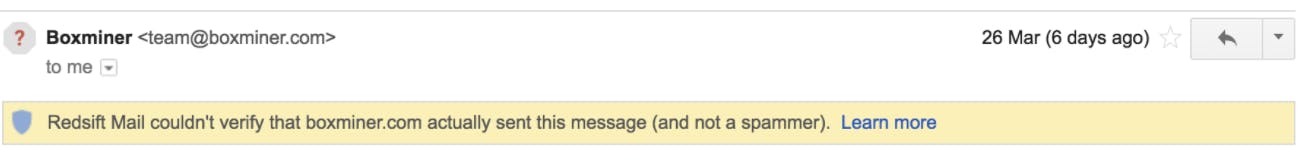
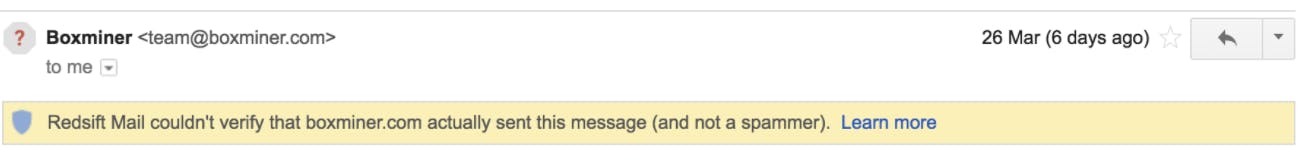
Some mailbox providers have started using visual signs in their mail clients to show if an email is authenticated. For example, Gmail displays a question mark (?) for unauthenticated emails - see the example below.
What is an SPF include statement?
An include is an SPF mechanism that points to a domain to be queried when checking if the sending IP is allowed or not. If the sending IP is part of the include then it results in a match and SPF passes.
For example, if you have include:_spf.google.com as part of your SPF record and the originating IP of an email is Google’s IP, it will result in a match as you have authorized Google to send on your behalf and the sending IP is found inside of the include mechanism.
What are SPF macros?
An SPF macro refers to a mechanism used in SPF records to define reusable sets of IP addresses. SPF macros enhance the flexibility and maintainability of SPF records by allowing you to define complex sets of IP addresses in a single mechanism, which can then be referenced within multiple SPF records. This can make it easier to manage large sets of authorized sending servers without duplicating the same information in multiple places.
For example, instead of listing individual IP addresses for each authorized email server in your SPF record, you can define a macro like this:
@spf.salesforce.com IN TXT "v=spf1 exists:%{i}.spf.mta.salesforce.com -all"
In this example, the macro is the %{i} mechanism, which calls the sender IP of the email. This means the domain becomes something like 233.124.65.65._spf.mta.salesforce.com.
Managing SPF this way allows you to control a large list of IPs without hitting the SPF lookup limit, and also obscures which IPs you approve for public querying.
The problem with SPF macros
The risk with SPF macros is that the majority of legacy email infrastructures do not support them, causing catastrophic deliverability issues. We know from technical studies and our own experience that only about 75% of SMTP servers get macros right.
If an email server does not support SPF macros, the behavior can vary as follows:
No expansion
If the receiving email server does not support SPF macros, it will not expand or process any macros referenced in the SPF record. Instead, it will treat the macro reference as a literal string. This means that the SPF record effectively loses its intended functionality, potentially leading to incomplete or inaccurate SPF checks. Though macros aren’t used in production SPF records, the no expansion behavior is used in email servers like iCloud.
Possible SPF failures
Depending on how the SPF record with macros is structured, the lack of macro expansion could result in SPF failures or 'Neutral' results (denoted by the ?all mechanism). In either case, it might not have the desired effect of properly authorizing legitimate sending servers.
Deliverability impact
If the SPF macros play a critical role in authorizing legitimate sending servers, emails might be more likely to fail SPF checks or be marked as suspicious by email receivers that rely on SPF for authentication.


